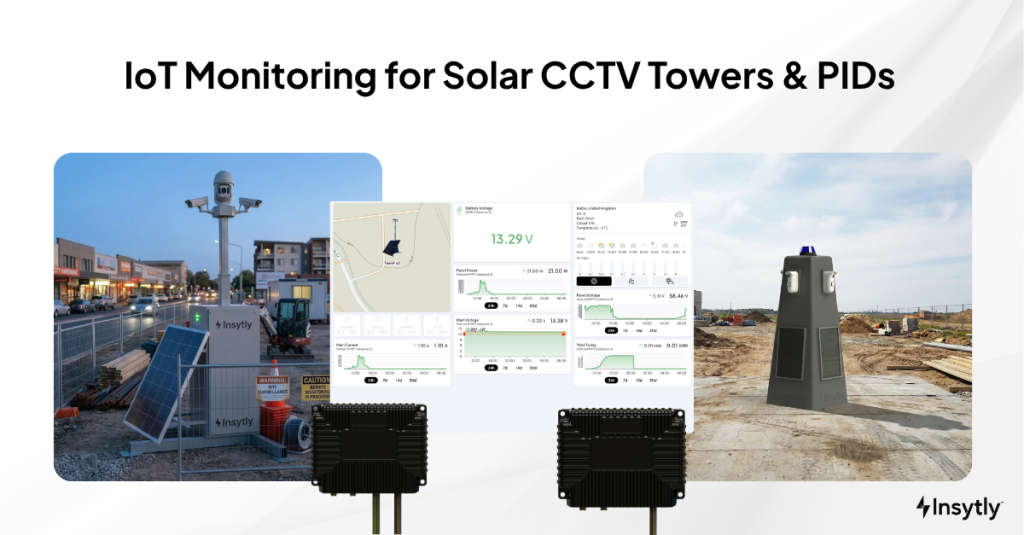
The Blueprint for Autonomous Security: IoT Monitoring for Solar CCTV Towers & PIDs
In brief: IoT monitoring for solar CCTV towers combines purpose-built, low-power telemetry hardware with cloud software. Together, they remotely track the power, connectivity, and health of off-grid security systems. This enables proactive maintenance, remote power-cycling, and remote diagnostics from a single unified platform - all without adding significant load to the asset's energy budget.
The rapid deployment security sector is experiencing unprecedented growth. National infrastructure projects, remote construction, and strict site security mandates are driving a surge in demand for temporary surveillance. At the same time, the industry has adopted solar and battery architectures to cut carbon and eliminate reliance on diesel generators.
However, this rapid evolution has exposed a critical operational vulnerability. Security integrators have solved the problem of powering remote sites. Many are now struggling with the logistical burden of managing them. Solar CCTV towers and PIDs require constant vigilance over battery health, location status, cellular connectivity, and hardware integrity.
The reality is that the vast majority of security companies currently have no dedicated monitoring at all. Their only visibility comes from checking whether cameras are online in the VMS. If the feed is live, the assumption is that everything is fine. If it drops, the only option is to send an engineer. There is no insight into why the system went down and no early warning. Meaning is no way to resolve the issue remotely.
The minority of operators who have recognised this gap have turned to fragmented, pieced-together solutions. These combine off-the-shelf IoT sensors with generic third-party software dashboards. This fractured approach creates its own problems: blind spots, API breakages, and a monitoring system that itself becomes a burden. Meanwhile, rising fuel and engineer callout costs are actively eroding the profit margins of poorly monitored or entirely unmonitored fleets.
The conversation must now shift from basic asset deployment to true infrastructure autonomy. This article examines the three stages of monitoring maturity and why purpose-built, end-to-end IoT monitoring is the definitive standard for the modern security fleet.
What IoT Monitoring for Solar CCTV Towers Means
IoT monitoring for solar CCTV towers and PIDs is the continuous, automated extraction of vital operational data from remote security assets. Edge-based telemetry hardware transmits real-time metrics — battery voltage, solar yield, router connectivity, and tamper status — to a centralised cloud platform.
Crucially, in a security context, advanced IoT monitoring is bi-directional. It goes beyond passive data observation to include remote control. Fleet operators can power-cycle a frozen PTZ camera, reboot an industrial 4G router, or trigger auxiliary lighting — all from a central control room, with no physical intervention at the edge.
The Three Stages of Monitoring Maturity
Most security fleet operators fall into one of three stages. Understanding where your operation sits is the first step toward cutting unnecessary costs and scaling with confidence.
Stage 1: No Dedicated Monitoring
This is the current reality for most of the rapid deployment security market. The operator’s only visibility is whether the camera feed is live in the VMS. If the feed is active, everything seems fine. If it drops, someone dispatches an engineer.
There is no insight into battery State of Charge, no record of solar yield trends, and no awareness of a router degrading before it locks up. The operator is entirely reactive — learning about problems only after they become failures.
This approach may feel manageable at small scale but it conceals costs that compound rapidly. Unnecessary site visits to cycle power on a frozen router. Emergency callouts for battery depletion that data would have predicted. SLA breaches from overnight failures that a single alert could have prevented.
Stage 2: Fragmented Telemetry
Operators who recognise the limitations of Stage 1 often try to build their own telemetry stacks. They buy generic IoT voltage sensors from hardware vendors and try to map that data into third-party platforms.
This approach fails on three fundamental levels.
First, generic IoT hardware is not built for remote security. It often lacks the 12V/24V relays needed to remotely reboot security peripherals. Many of these generic devices also draw significant power. The Victron Cerbo GX, for example, was built as a solar installation monitor — not a low-power edge telemetry device. In an off-grid environment, every watt of solar harvest must go to critical security loads. A monitoring device that consumes substantial energy works against the system. Purpose-built telemetry hardware operates on a fraction of the power.
Second, firmware updates from separate hardware and software vendors inevitably break API connections. This leads to missing data and dashboard outages.
Finally, fragmented stacks create a “support vacuum.” When the monitoring system fails, the software provider blames the hardware. The hardware provider blames the software. The integrator is stuck in the middle, forced to send an engineer for an issue they cannot diagnose remotely.
Stage 3: Purpose-Built, End-to-End IoT Monitoring
The third stage eliminates the compromises of both previous approaches. The same team engineers the telemetry hardware and the cloud platform, purpose-built for off-grid security. The hardware draws only milliamp-hours during active reporting windows. It never competes with cameras, analytics, or comms equipment for the asset’s finite energy budget.
This is not an incremental improvement on Stage 2. It is a fundamentally different architecture, with bi-directional control, firmware-to-cloud synchronisation, and single-point accountability. Along with a power footprint so low that adding monitoring extends the system’s intelligence without reducing its runtime.
The Operational Reality: What a Blind Dispatch Actually Costs
Inadequate monitoring, or no monitoring at all, creates a daily financial drain. Consider what this looks like for a rapid deployment security operator.
A PID system protecting a remote solar farm goes offline at 3:00 AM on a Sunday. The central monitoring station loses the camera feed.
Without purpose-built IoT monitoring (Stage 1) or with fragmented tools that lack remote actuation (Stage 2), the operator faces a blind dispatch. They do not know if:
- The cellular router has simply frozen and needs a hard reboot.
- The solar yield was insufficient, and the battery bank has depleted.
- The unit has been physically vandalised or tampered with.
The operator’s only protocol is to dispatch an engineer. The engineer drives two hours to site in a diesel vehicle. The router had simply locked up. The engineer flips a switch, reboots it, and drives two hours back.
This single event consumes hours of labour, burns expensive fuel, and leaves the perimeter vulnerable. Operators consistently report that one site visit to reboot a router often costs more than an entire year of dedicated IoT monitoring.
Real-world proof point: A recent deployment in Scotland maintained 100% uptime with zero engineer callouts across 39 consecutive days, even as solar yield collapsed 99% in just three days.
Structural Causes of the Problem
The blind dispatch persists because of structural issues in the security supply chain.
The Hardware-Software Divide
Very few companies can design both industrial-grade, low-power edge hardware and enterprise-grade cloud software. The market is therefore full of companies that specialise in only one half. This forces integrators to bridge the gap themselves using custom scripts and fragile integrations.
Focus on the Payload, Not the Platform
The security industry has always focused on the “payload”; cameras, analytics, and sirens. Power and connectivity were afterthoughts. Telemetry was a luxury, not a structural necessity. For many operators, the idea of monitoring the platform that powers the cameras is still a novel concept.
The Power Consumption Blind Spot
When operators do add monitoring, they rarely consider its energy footprint. Devices built for grid-connected solar installations introduce a parasitic load. In winter, when solar yield is lowest and every watt-hour counts, a power-hungry monitor can be the difference between survival and total battery depletion.
Lack of Remote Actuation
Many early telemetry systems were “read-only.” They could warn an operator about a dying battery. They lacked the relay architecture to do anything about it. Without remote load-shedding or power-cycling, these systems were just early warnings for an inevitable site visit.
Consequences for Companies
Operating at Stage 1 or Stage 2 creates severe commercial risks.
Margin Erosion via Logistical Debt: Hardware pricing is a race to the bottom. Operational efficiency determines profitability. A spike in fuel costs can rapidly consume the profit margin on every manually maintained asset.
SLA Breaches and Reputational Damage: Tier-1 clients demand uninterrupted uptime. A tower that dies overnight from predictable battery depletion falls on the integrator.
Scaling Bottlenecks: No company can scale from 50 towers to 500 with site-by-site manual diagnostics. The operational overhead becomes unsustainable.
Hidden Energy Costs: Stage 2 operators may not realise their monitoring hardware consumes a meaningful share of the daily solar harvest. Across hundreds of towers, that cumulative energy loss reduces system resilience and increases downtime risk.
What Fleet Operators and Ops Directors Actually Need
Fleet managers do not need generic IoT platforms cobbled together from overseas components. Nor do they need to keep flying blind. They need purpose-built, autonomous infrastructure tools:
- True End-to-End Accountability: The edge hardware and cloud dashboard must come from the same in-house team. This eliminates API breakage and gives operators a single point of support.
- Low Power Consumption: The hardware must draw milliamp-hours per reporting cycle, not continuous watts. It must never compete with the security payload for energy. This is non-negotiable for winter resilience.
- UK-Designed and UK-Manufactured Reliability: Supply chain transparency matters in security. UK-built hardware paired with UK-developed software ensures rapid R&D, secure data handling, and same-timezone support.
- The Hub + API Architecture: A proprietary IoT hub handles core battery and solar metrics. Open-API cloud modules pull in third-party data (fuel cells, routers, alarms) into a single pane of glass.
- Remote Power Cycling: The ability to remotely reboot specific 12V/24V channels from a desk. This single capability eliminates most blind dispatches.
The Monitoring Maturity Spectrum
The rapid deployment sector spans three distinct operational stages. The table below outlines how each stage performs against the metrics that determine fleet profitability and scalability.
Operational Metric
Stage 1: No Dedicated Monitoring
Stage 2: Fragmented (Pieced-Together) IoT
Stage 3: Purpose-Built End-to-End Ecosystem
Visibility
Camera feed online/offline only. No power, battery, or connectivity data.
Partial data via third-party sensors mapped to generic dashboards.
Full telemetry: battery, solar, connectivity, location, tamper — in a single platform.
Diagnostic Action
Blind dispatch for every fault.
Read-only data; most alerts still require physical site visits.
Bi-directional; allows remote power-cycling and load shedding.
Power Footprint of Monitoring
N/A (no monitoring hardware installed).
High risk: repurposed hardware may draw continuous watts, reducing system runtime.
Low: purpose-built hardware consuming milliamp-hours per reporting cycle.
System Stability
N/A.
High risk of data loss due to third-party firmware/API updates.
Guaranteed stability; firmware and cloud updates are synchronised by the same team.
Technical Support
No telemetry support to call.
Finger-pointing between hardware vendor and software vendor.
Single point of accountability and rapid support resolution.
Scalability
Unsustainable beyond small fleets.
Fragile at scale; each integration adds complexity.
Architected for fleet-wide deployment with centralised control.
Industry Shift: From Reactive Maintenance to Proactive Autonomy
The security industry is moving from Reactive Maintenance to Proactive Autonomy.
Most fleet operators are still at Stage 1. They rely on camera feeds as their only health indicator, but clients now demand guaranteed uptime. To deliver this while protecting margins, leading fleets are leapfrogging Stage 2 entirely. They are adopting purpose-built monitoring from the outset: a “Zero Call-Out” methodology.
This shift is reshaping procurement. Integrators now demand that every field asset ships with native, bi-directional telemetry that does not compromise the energy budget.
A New Category of Solution: The End-to-End Visibility Layer
So what does this ecosystem actually look like in practice?
Security fleets need a solution that eliminates both the hardware-software divide and the power consumption blind spot. This is the True End-to-End Data Visibility Layer.
This category of solution is purpose-built for off-grid security. The same team engineers the low-power telemetry hub inside the tower and the fleet management dashboard used by the ops team. Data transmission is flawless and low-latency, with no meaningful load on the asset’s power system.
A true visibility layer also acts as an aggregator. Bespoke edge hardware pairs with an open-API cloud architecture. Operators can pull in data from third-party smart hardware (e.g., power controllers, cellular routers) into a single view.
This end-to-end approach lets operators monitor battery health, track network stability, and execute remote reboots. It does all of this while consuming a fraction of the energy of repurposed alternatives. It removes the friction of third-party integrations, provides a single point of control, and lets security companies guarantee relentless uptime for their clients.

Conclusion
Solar CCTV towers and PIDs have revolutionised remote security. But managing these assets at scale introduces challenges that most companies are not yet equipped to handle. Most of the market still operates blind, relying on camera feeds and absorbing the cost of every blind dispatch.
Those who have sought a solution face a different set of risks. Fragmented telemetry stacks bring API breakages, support vacuums, and monitoring hardware that drains the very system it should protect.
The path forward is clear. Purpose-built, end-to-end monitoring ecosystems — where low-power hardware and cloud software come from the same team — are the definitive standard. By moving directly to Stage 3, fleet operators achieve true infrastructure autonomy. They transition from reactive firefighting to profitable, proactive control.
About Insytly
Insytly is the UK-designed, end-to-end IoT monitoring platform built for off-grid security. The same in-house team engineers the IY-HUB2 telemetry hardware and the cloud dashboard. This gives fleet operators remote power-cycling, real-time battery intelligence, and a single pane of glass across their entire fleet.
One team, one platform, total visibility.
Visiting The Security Event (TSE) 2026 in Birmingham? Come and see the platform live on our stand.
